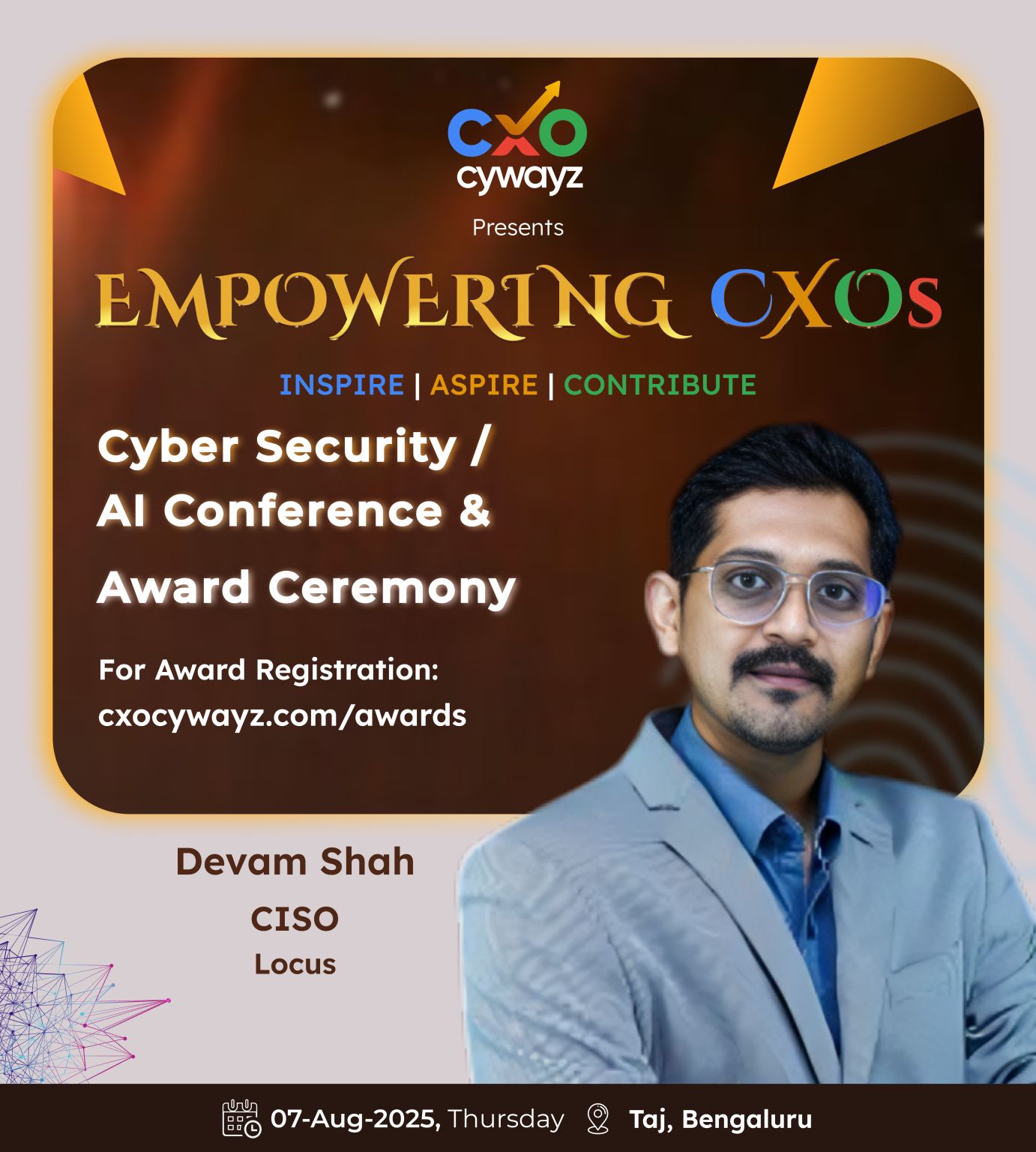
Locus (Ingka Group | IKEA)
Leading AI security, AI governance, privacy, and compliance for a cloud-native logistics AI platform serving 1.5B+ deliveries across 30+ jurisdictions. Established AI security governance with LLM guardrails, AI DPIAs, and AI TPRM aligned to NIST AI RMF and ISO/IEC 42001. Delivered SOC 2 Type II. Led post-acquisition security due diligence for Ingka Group (IKEA), driving remediation of 70,000+ SAST/SCA/OSS vulnerabilities (current-role scope). Lean team of 5, $1M budget. Reduced late-stage vulnerabilities by 96%.
SOC 2 Type IIAI GovernanceLLM SecurityNIST AI RMFISO 42001GDPRAgentic AI
Teachmint
Led IT, Security, Privacy, and Compliance for a global edtech SaaS platform supporting 35M+ student records across 33 countries. Built the entire AppSec pipeline using open-source tooling (Semgrep, Trivy, OWASP ZAP, SonarQube) — eliminating enterprise licensing. Secured AI-enabled IoT ecosystem across 600+ schools with 4,500+ smart classrooms powered by 15,000+ customized devices.
35M+ RecordsOpen-Source AppSecCISO of the YearGDPR/COPPAIoT Security
Byju's Great Learning
Established global security and privacy across 100+ countries, 2,000+ employees, and 5,000+ contracted teachers. Led security integration during Byju's acquisition, aligning strategy with 300% annual growth. Deployed company-wide Zero Trust architecture. First-time ISO 27001 & ISO 27701 certifications enabling 50+ enterprise B2B deals with global banks, Big4, and Big Tech.
100+ CountriesZero TrustISO 27001/2770150+ B2B DealsM&A Integration
Meditab Group of Companies
Appointed by Group Chairman to stabilize the organization during a major security crisis — managing a large-scale PHI breach and ongoing ransomware incidents. Built and led global security teams across 3 geographies (25+ professionals, 24x7 SOC). Secured OT/IoT environments for pharmaceutical robotics (30+ robotic platforms, 1,000+ sensors per system). Achieved HITRUST i1, SOC 2 Type II, ISO 27001, ISO 27701, and HIPAA.
Crisis LeadershipPHI BreachRansomwareOT/IoT RoboticsHITRUST5,000+ Workforce
Tata Consultancy Services
Enterprise security governance and architecture across TCS data centers, cloud environments, and critical infrastructure — including the EKA supercomputer used for Indian defense and space research. Key role in corporate security modernization across 1,000+ remote offices. Enterprise incident response for critical infrastructure environments.
TCSDefense & Space1,000+ OfficesEKA SupercomputerZero Trust